This one, wow what a pain in the a******
It took me hours to finally debug this issue.
Had setup NPS on a Windows 2019 server, like many times before, registered it in the Active Directory, and installed the Use Azure AD Multi-Factor Authentication with NPS – Azure Active Directory | Microsoft Docs” plugin, setup the policies in NPS and all good, then I setup my radius client device, in this example a Sophos XG firewall, but no! – nothing worked, after som debugging I saw this on the Windows server event log:
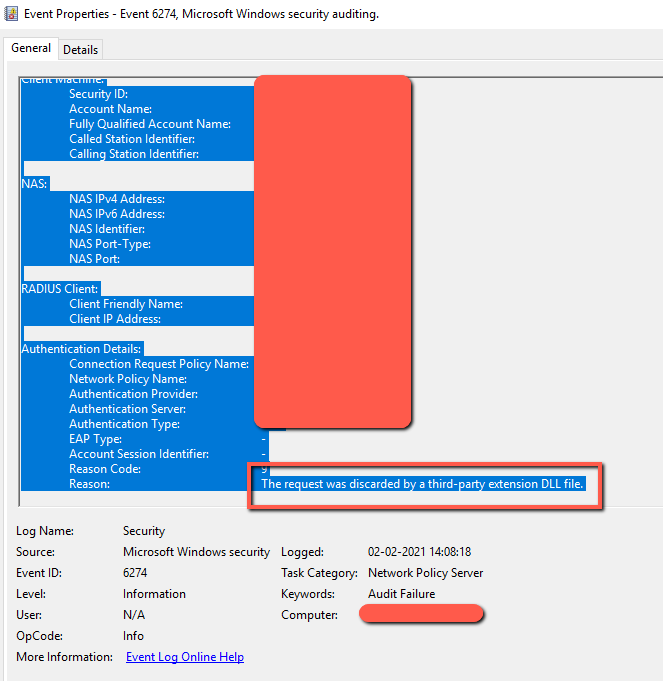
So it was clear that the NPS extension module rejected it, but why?
Luckily this guy at “Sergii’s Blog” did some debugging with the extension in some other matters, and he found out why:
Looking at Azure AD portal – go to Enterprise Applications – Change the Application Type to All, search for Azure Multi-Factor Auth Connector and Azure Multi-Factor Auth Client, you will find theese guys:

in my example the ” Azure Multi-Factor Auth Client” was disabled, did not know why!!:
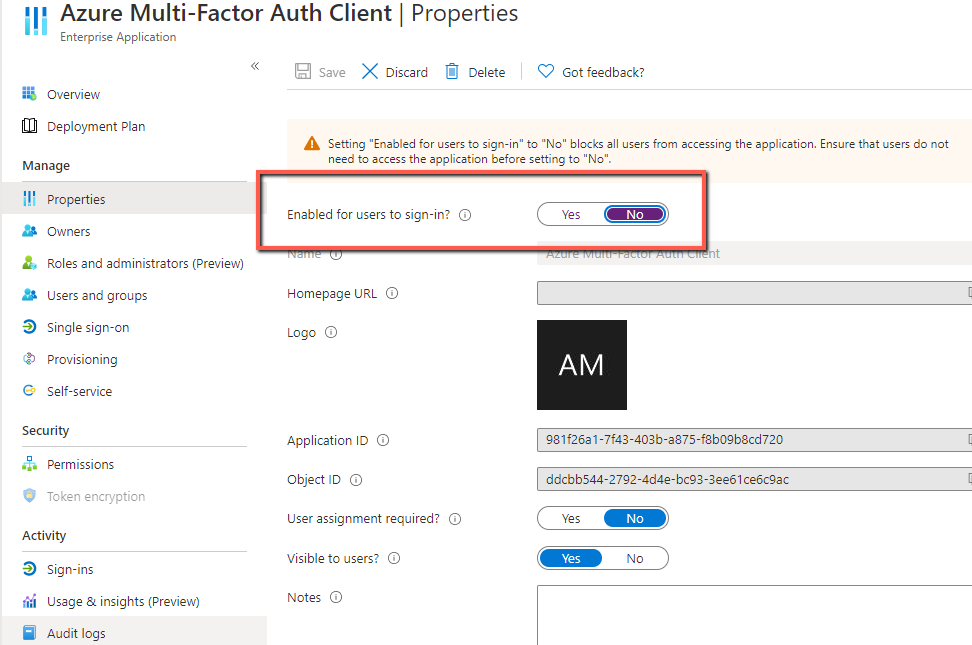
Just enable and save, check the other multifactor also. Right after this, the NPS MFA Extention worked perfectly.
Many many thanks to “Sergii’s Blog” for pointing in the right direction 🙂