Inspiration for this post was taken from: https://rieskaniemi.com/azuremfa-nps-extension-with-sophos-utm-firewall/
Some of the things that I’ve seen at work, is that Sophos UTM VPN users are using one token for Sophos SSLVPN and another for ex. Office 365 services. Both tokens can be in Microsoft Authenticator, but only the one that Office 365 is using, can do the “pop-up”, letting the user easy sign-in, like this:
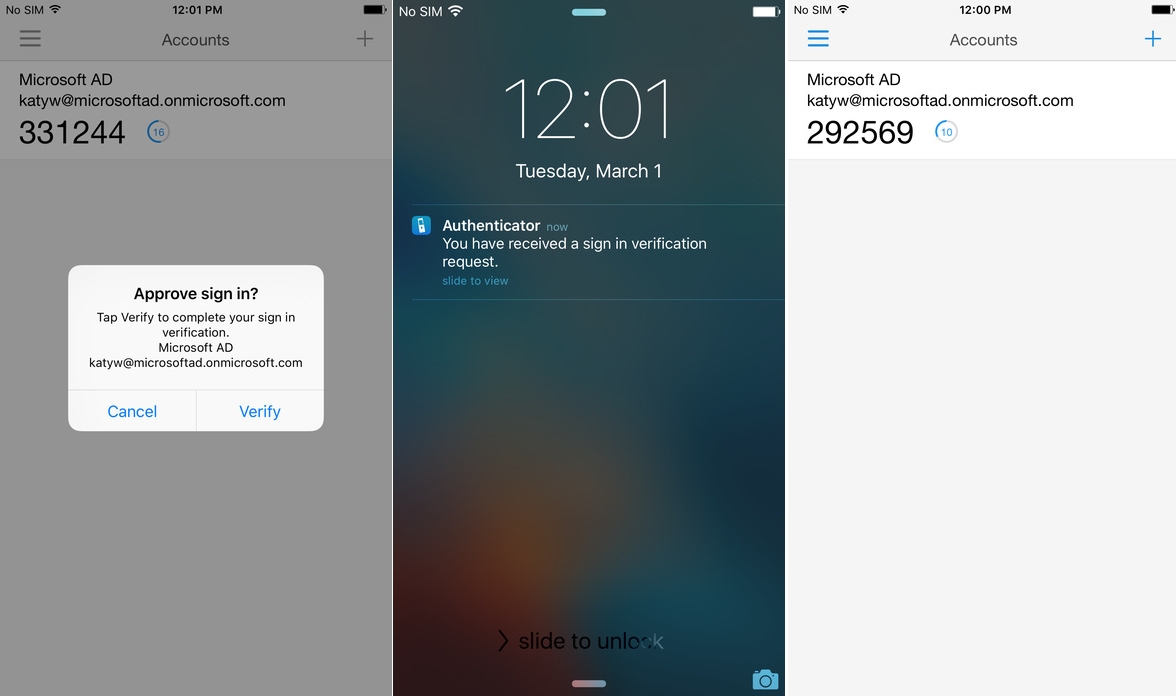
Nonetheless it’s easier for the IT dept. (and the user!) to maintain only one token solution 🙂
Here is the auth flow for Azure MFA with NPS Extension:

Nice isn’t it 😉
So how to fix?
We setup Sophos UTM for RADIUS validation for SSLVPN and UserPortal access, and if you use the built-in OTP solution, disable that 🙂
To get started:
- If you do not have MFA enabled for your Office 365/Azure AD account’s you can enable it through following link: https://aka.ms/mfasetup
- And of course you need to have set Azure AD Connect to get your on-premise talking with Azure, I will not go into the details with this here, as I assume this is already setup and working 🙂
Let’s go:
- Install the Network Policy Server (NPS) role on your member server or domain controller. Refering to the Network Policy Server Best Practices, then you will find this “To optimize NPS authentication and authorization response times and minimize network traffic, install NPS on a domain controller.” So we will go ahead and place this on the domain controller, but remember it’s also possible to do it on a domain joined member server!

Press “Next” and the installation begins:
- After installation has ended, go and join the NPS to the Active Directory, right-click NPS (Local):

- Download and install the NPS Extension for Azure MFA here:
https://www.microsoft.com/en-us/download/details.aspx?id=54688Note: As i did try this on a server with already setup NPS, it failed with the other mechanisms, because of this:
https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-mfa-nps-extension#control-radius-clients-that-require-mfa“Control RADIUS clients that require MFA
Once you enable MFA for a RADIUS client using the NPS extension, all authentications for this client are required to perform MFA. If you want to enable MFA for some RADIUS clients but not others, you can configure two NPS servers and install the extension on only one of them.
Configure RADIUS clients that you want to require MFA to send requests to the NPS server configured with the extension, and other RADIUS clients to the NPS server not configured with the extension.”
So the “workround” is to run the MFA for the Sophos on a seprate NPS instance ?
- After it’s installed, go and follow the configure is like it’s stated here (Find TenantID and run Powershell script):
https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-mfa-nps-extension#azure-active-directory - Go and configure your radius Client, here it’s the UTM:

Remember the secret, we need it later on 🙂 - Create a “Connection request policy”:


See above the NAS Identifier, it’s “ssl”, it’s taken from this scheme:
Found here: https://community.sophos.com/kb/en-us/116144Just set like above, and the rest of the settings, just leave them to their defaults 🙂
- Now create a “Network Policy”
 Add a domain group, that shall have this access, to simplify, here I have choose domain\Domain Users
Add a domain group, that shall have this access, to simplify, here I have choose domain\Domain Users
Now the EAP types, UTM does only support PAP, as far as I have tested:
You will get a warning telling you that you have choosen unencrypted auth (locally – not on the Internet!), just press OK.
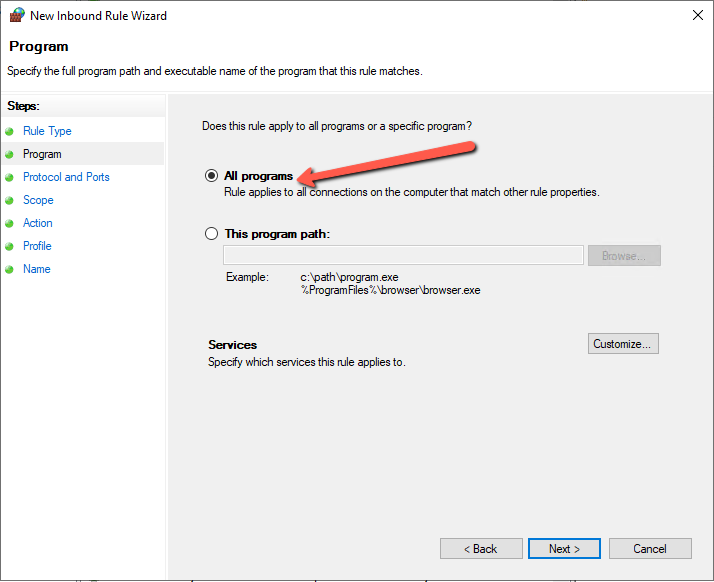
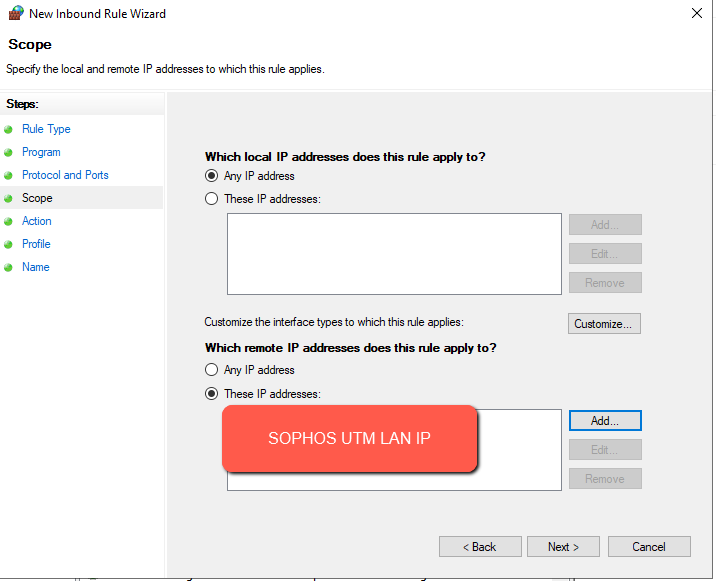
Just left the rest to their default’s and save the policy. - Now to create a firewall rule:


- Now to setup the UTM for this:

Add new Authentication server:
Remember to choose RADIUS:

Fill in as your environment matches:
Type in the secret you wrote down earlier and create a host object for your NPS, also remember to change the timeout from 3 to 15 secs!
You can now test is the authentication through NPS and Azure MFA is working, change NAS-Identifier to “ssl” type in a users username (e.mail adress) and password, and your phone should pop-up with Microsoft Authenticator 🙂
- Now to grant the RADIUS users access to SSL-VPN

Just add the built-in object “Radius Users” to your SSL-VPN profile:

- Now login to the User Portal and download a VPN client (You cannot use the old ones, if you already had thoose installed)
- Now connect through VPN, type in your full email in username and your password, then wait for MS Authenticator to pop-up, accept the token and you are logged into VPN 🙂
UPDATE: 20/11-2023
Due to recent changes in the module and Entra, you will need to add this in the registry of the NPS server:
- On the NPS Server, open the Registry Editor.
- Navigate to HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AzureMfa.
- Create the following String/Value pair:
- Name: OVERRIDE_NUMBER_MATCHING_WITH_OTP
- Value = FALSE
- Restart the NPS Service.

Sources:
https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-mfa-nps-extension-vpn
https://docs.microsoft.com/en-us/windows-server/networking/technologies/nps/nps-best-practices





Great job, thank you very much.
Thanks Thorsten 🙂
This is great but got stuck on error when testing from UTM. I have timeout set to 15 seconds, and tried 30 seconds too. Google hasn’t been much help – “failed to recv packet from radius server: timed out waiting for packet” – any pointers appreciated. thx!
Hi, thanks for your reply 🙂
As the errer states, the RADIUS server does not respond, so check:
1) Firewall rules on the radius server
2) Have you setup the correct radius secret and corret UTM IP on the radius server? 🙂
Yes, I have everything set but get this in Event Viewer->Security Events:
Network Policy Server discarded the request for a user.
Contact the Network Policy Server administrator for more information.
User:
Security ID: AD\testaccount
Account Name: testaccount@{mydomain}.com
Account Domain: AD
Fully Qualified Account Name: ad.{mydomain}.com/{myAD}/Users/Test Account
Client Machine:
Security ID: NULL SID
Account Name: –
Fully Qualified Account Name: –
Called Station Identifier: –
Calling Station Identifier: –
NAS:
NAS IPv4 Address: –
NAS IPv6 Address: –
NAS Identifier: ssl
NAS Port-Type: –
NAS Port: –
RADIUS Client:
Client Friendly Name: Sophos UTM
Client IP Address: 10.0.0.1
Authentication Details:
Connection Request Policy Name: Use Windows authentication for all users
Network Policy Name: Sophos UTM Network Policy
Authentication Provider: Windows
Authentication Server: OS-DC-01.ad.{mydomain}.com
Authentication Type: PAP
EAP Type: –
Account Session Identifier: –
Reason Code: 9
Reason: The request was discarded by a third-party extension DLL file.
After posting I noticed the connection policy being used. I have two policies. I disabled the ‘use windows authentication for all users’ policy and now the event log just has a blank value instead of my enabled’Sophos UTM Policy’. and the Reason code has changed to 21 with “An NPS extension dynamic link library (DLL) that is installed on the NPS server rejected the connection request.”
I figured this out. I had to add users to the Azure Multi-Factor Authentication app in Azure AD Enterprise apps. It had no members by default.
Hi John,
Great debugging skills, thanks for sharing 🙂
Hi Martin,
thanks for this how-to. great work.
one question though:
i see that this is working with the MFA app confirmation, but is it also possible to use the generated 6-digit code of the authenticator app?
just in case you might not have internet access with your smartphone or not every use has setup the confirmation via the app turned on.
Thank you!
Hi, No unfortunately, as the NPS extension works as shown at the top 🙂
Hi Good article.
I have followed all steps but am running into an error. The MFA app confirmation is working, but the openvpn client is saying wrong credentials:
Fri Apr 02 14:44:24 2021 SENT CONTROL [name]: ‘PUSH_REQUEST’ (status=1)
Fri Apr 02 14:44:24 2021 AUTH: Received control message: AUTH_FAILED
Fri Apr 02 14:44:24 2021 SIGUSR1[soft,auth-failure] received, process restarting
Fri Apr 02 14:44:24 2021 MANAGEMENT: >STATE:1617367464,RECONNECTING,auth-failure,,,,,
Fri Apr 02 14:44:24 2021 Restart pause, 5 second(s)
Any ideas?
Hi,
Firstly you need to download new vpn config to use this, you cannot use the old profile, login is then your full email address and AD password.
Have you done that? 🙂
Regards Martin
Very strange, when adding the UPN as user in my Sophos it worked. Now (few days later) it also works without the UPN. Maybe a timing/syncing issue.
BTW, this also works for a OpenVPN AS environment.
Again: Great article!
Just glad to hear it worked, it was the “Azure-wait-time” you was hit by 😀
Thanks!
Br. Martin
Thanks for sharing, the authentication works great.
But: The email Attribut is not available throught Radius(NPS) authentication. Which causes the Sophos to delete the email address of any user, which authenticates throught Radius. Now the users can’t white-/black list and release mails.
Did you experience the same behaviour or did I miss something?
Thanks 🙂
Hmm..No I have not, have you set to create users automatically, and do fetch from AD at daily basis?
Yes, we fetch the users from AD.
Hmm weird.
Management –> Authentication Services –> [Global pane] –> Create user aut. enabled + Automatic User Creation for Facilities enabled for end-user portal, are thoose set?
I have no issues.
yes, both set.
Have you enabled “Active Directory Group Membership Synchronization” or “Prefetch Directory Users” in Authentication Services -> Advanced?
I think it could be one of them, which wipes the email addresses.
Only “Prefetch Directory Users” is set 🙂
usually we have a security group, where ssl vpn users are synced to sophos. They are created as john.doe and have all the email adresses.
when we now use radius authentication with azure mfa then a new user with upn adress is created: john.doe@upn.com (we use upn to log into o365/azure services) this user has no email addresses and cannot use anti-spam features of user portal etc.
now i created a deny network policy on this new radius, where users with ad syncd accounts to sophos like john.doe (who are a member of our standard ssl vpn group synced to sophos) are not allowed to use the mfa function.
hence i think we have to decide if we want radius authentication or ad authentication with anti-spam user portal features, because syncing a radius user afterwards with ad to get the mail adresses will not be possible i guess
This is a great article. I have hit a snag though. the NPS is working and the authenticator asks for the MFA just fine when attempting to connect to the VPN, however it says that AUTH failed. the test works fine in the setup, but after downloading the VPN config and installing it, it just keeps prompting for authentication. Here is the log from the VPN client:
SENT CONTROL [My Name]: ‘PUSH_REQUEST’ (status=1)
AUTH: Received control message: AUTH_FAILED
SIGUSR1[soft,auth-failure] received, process restarting
MANAGEMENT: >STATE:1634320138,RECONNECTING,auth-failure,,,,,
Restart pause, 5 second(s)
Any help would be appreciated. Thank You
HI,
Do you have more than the radius server in the authentication section of the firewall?
When you download the vpn client, you MUST use your full email address?
Any luck ?
Dear Martin,
Thank you for your great article. We have this set-up and are testing now. It works fine. To implement this further we came across an issue that we losing the option to restrict access to network resources (per SSL VPN profile). We have several SSL VPN profiles (staff, external/hired staff and suppliers); some with very limited access.
This all because the radius users is a general user group.
Do you know a way how we can still differentiate grant / access per (AD user)group by using 1 SSL VPN profile?
What do you do for users that already are using vpn. do you just have them redownload\reinstall the client? or will it autoupdate the new policy?
Thanks
They have to re-download as they use full email not and not the initials anymore 🙂
Great Post, thanks a lot. We successfully deployed MFA with Sophos.
We need to change some things:
1. We had to use client IP instead of NAS IP as condition in Connection Request
2. We removed nas identifier ssl, because User cannot login to User Portal to get their profiles
3. We added radius user to user portal access as well
Dear Martin, thank you for your great work and sharing your knowledge, now users have mfa for html5-vpn-portal, greetings from switzerland
Thanks 🙂
Br. Martin