When you have your Remote Desktop farm spinning with connection broker and the right certificates, all should be over with the certificate warnings…..ehh should??
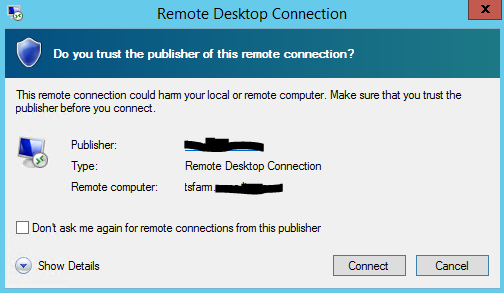
You create a RDP profile for your users, so they have a shortcut on their desktops for the RD farm, but they get this screen:

But did i just not install certificates on my connection broker and all my RDS hosts?!
YES
But when I just open the remote desktop connection client (mstsc.exe) and type in the fqdn of my tsfarm I get no errors?!
CORRECTLY
What’s wrong then?
When you SAVE the RDP file, with all the settings, the file itself is not signed in any way, and therefore not trusted!
Luckily Microsoft has made RDPSIGN which come to aid!
You go to your server, where you have already installed the certificates in the Personal Certificate store, you open the certificate, and find it’s thumbprint:

You copy paste that thumprint above, and go to your command prompt and type:
rdpsign /sha1 <hash> <your-rdp.file.rdp>
UPDATE: 25/7-2018:
RDPSIGN is updated and now want’s a SHA256 option in stead:
rdpsign /sha256 <hash> <your-rdp.file.rdp>
is your certificate is new, you can just use the sha1 value from the thumprint, it works either way 😉
And thats it!
Distribute the file to your users by mail or script, and when they try to connect the next time, they will see this:
Now they can just check the “Don’t ask me” dialog, but not worry about a “dangerous” publisher 🙂




Hi,
this does not work on my server 2012r2.
It says that all rdp files were signed, but the “publisher cannot be identied” pops up .
How can I check that the rdp file is signed?
HW
Hi, thanks for the article. Am I right I have to resign the RDP File every time I replace my purchased certificate? Thank